SolarWinds has released a hotfix that addresses two critical vulnerabilities, one of which allows for remote code execution and the other for hardcoded credentials. These vulnerabilities, identified as CVE-2024-28986 and CVE-2024-28987, have been fixed in WHD 12.8.3 Hotfix 1, ensuring the integrity and confidentiality of customer data.
CVE-2024-28986: Broken Access Control Remote Code Execution
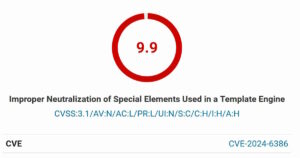
The first vulnerability, CVE-2024-28986, is a Broken Access Control Remote Code Execution vulnerability that could allow an attacker to run commands on the host machine. Although SolarWinds was unable to reproduce the vulnerability without authentication, the company has taken a proactive approach by releasing a patch to prevent potential exploitation. This vulnerability has been assigned a severity rating of Critical, with a CVSS score of 9.8.
CVE-2024-28987: Hardcoded Credential Vulnerability
The second vulnerability, CVE-2024-28987, is a Hardcoded Credential vulnerability that allows remote, unauthenticated users to access internal functionality and modify data. This vulnerability has been assigned a severity rating of Critical, with a CVSS score of 9.1. The hardcoded credential vulnerability was discovered by Zach Hanley, who reported the issue in a responsible manner and worked with SolarWinds’ security, product, and engineering teams to fix the vulnerability.
What’s Included in the Hotfix
According to SolarWinds, the hotfix includes several key fixes, including:
- Resolving the SolarWinds Web Help Desk Hardcoded Credential vulnerability
- Adding more patterns to fix an SSO issue
- Restoring missing Upload Attachments, Cancel, and Save buttons in the client application
- Including fixes from 12.8.3 Hotfix 1, which resolve the SolarWinds Web Help Desk Broken Access Control Remote Code Execution vulnerability