A new authenticated command injection vulnerability CVE-2025-50989 has been disclosed for OPNsense 25.1, a popular open source, FreeBSD-based firewall and routing software developed by Deciso.
The flaw is triggered when the span POST parameter is concatenated directly into a backend system command without proper sanitization. The result is arbitrary command execution with web service privileges. In most OPNsense deployments, this privilege level equates to root.
This vulnerability requires valid administrative credentials. However, once leveraged, it grants complete control of the firewall — a particularly dangerous scenario given OPNsense’s frequent role as a core network security boundary.
Command injection flaws in administrative interfaces are not new, but their implications in firewall appliances are severe. OPNsense, like its sibling pfSense, is widely deployed in enterprise, ISP, and managed service provider environments.
While exploitation requires authentication, that barrier is often overestimated. Credential theft through phishing, keylogging malware, or lateral movement from a compromised internal host is common in targeted intrusions. Once an actor obtains administrator access, this vulnerability becomes a direct path to command execution and persistence.
Historically, similar authenticated flaws in perimeter devices have been exploited by both state-linked APTs and financially motivated ransomware crews. The presence of an RCE primitive on a firewall should be treated as a high-risk enabler for post-compromise escalation.
In order to exploit this vulnerability, The attacker must first obtain administrative credentials. This could be through credential stuffing (if the admin reused passwords), theft of VPN credentials, exploitation of another internal system, or insider misuse.
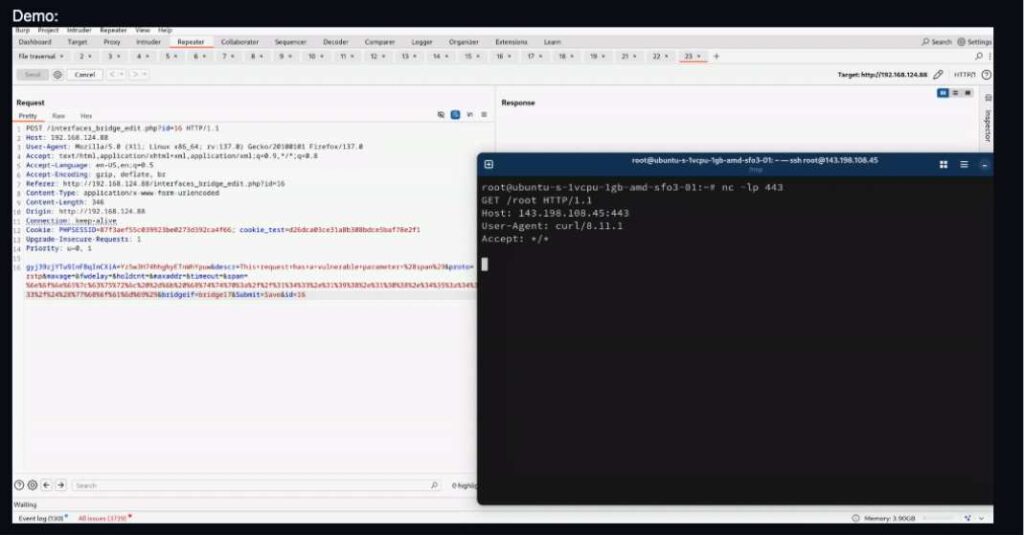
Once logged into the web interface, the attacker submits a crafted POST request to /interfaces_bridge_edit.php. The vulnerable span parameter is directly concatenated into a shell command invoked by the backend. This allows the injection of shell metacharacters (;, |, &&) and arbitrary commands.
Post-exploitation, the attacker can install backdoors or cron jobs on the OPNsense host, ensuring continued access even if credentials are rotated.
If exploited, attacker will gain root-level access on a firewall, pivoting becomes trivial. The attacker can intercept internal traffic, modify firewall rules to create hidden tunnels, deploy packet capture utilities to harvest additional credentials and redirect DNS or proxy outbound traffic to attacker-controlled infrastructure.




